Relevant Technology • Raving Results®
Our Locations | 501.603.3000501.603.3000 | Client Login
- Office
Equipment - Print
Management - Document
Management - Managed IT
Services - VoIP Phone
Systems - About
- Blog
- Contact
-
Support
Relevant Technology • Raving Results®
Our Locations | 501.603.3000501.603.3000 | Client Login
The journey to HIPAA compliance and security goes much further than a one-time risk assessment.
2018 Cost of Data Breach Study: Global Overview - IBM Security and Ponemon Institute
Your journey to HIPAA Compliance is an ongoing journey. It begins with a Risk Analysis, the foundation of any HIPAA Compliance Plan. It continues by gathering necessary tools and implementing specific processes that monitor, manage and mitigate both internal and external threats across today’s tumultuous cybersecurity landscape.
Any healthcare organization is at risk, regardless of size. According to HealthIT Security, “78 percent of healthcare providers reported that they experienced a healthcare ransomware or malware attack in 2017.” Given the threat of attack, and the monetary losses associated with HIPAA non-compliance fines or data breach, what is your organization waiting for?
A Managed Compliance Services Agreement helps assure HIPAA Compliance today and into the future. Through a thorough assessment process, visual intelligence and reporting, and continued workforce education, your healthcare organization can trek forward confidently through your HIPAA Compliance journey ahead.
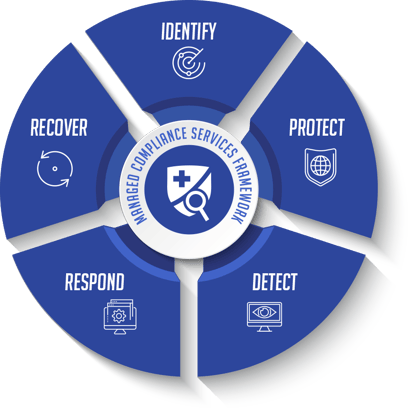
MCS Best Practices: Identifying your assets, protecting your assets, detecting incidents, responding with a plan, and recovering normal operations.
Covered entities must ensure that they have a current HIPAA business associate agreement in place with each of their partners to maintain PHI security and overall HIPAA compliance.
A Security Risk Analysis will uncover details regarding the compliance of outside vendor partnerships, as well as demonstrate your organization’s compliance with the required regulatory requirements of HIPAA and HITECH.

Should a data breach occur, the HIPAA Breach Notification Rule requires all healthcare organizations that experience an ePHI security breach to adhere to a strict breach notification process.
Access to your compliance portal will demonstrate your organization’s adherence to appropriate policies and procedures, as well as provide an ongoing vulnerability scan to mitigate and report future security threats.
The Office of Civil Rights (OCR) requires that covered entities identify vulnerabilities to ePHI that is collected, stored, processed or transmitted.
A Technical Vulnerability Assessment identifies both internal and external security gaps, as well as provides a thorough wireless assessment to identify any and all technical security weak points.

Employee negligence remains a main security concern for healthcare executives.
The online and onsite training available through a Managed Compliance Services program offers organization-wide communication methods and training tools, so employees inside your organization can confidently navigate their workday utilizing best practices.
The journey starts here. Our FREE eBook poses eight crucial questions to help your healthcare organization assess your current strategies and challenges, as well as determine whether it's time to take a hard look at Managed Compliance Services. What's your next step toward long-term compliance and security?
CLICK on the following link for 8 questions you should ask yourself.



Note: Various references and content within are from Konica Minolta and All Covered Brochures: Risk Management Program Through HIPAA Consulting Services From Konica Minolta, Healthcare IT Services And Solutions and Presentation: HIPAA Risk Assessment.

Datamax Inc. (Little Rock)
7400 Kanis Road
Little Rock, AR 72204
Main: 501.603.3000 (Contact)
Datamax Inc. (Hot Springs)
317 3rd Street
Hot Springs, AR 71913
Main: 501.624.4469 (Contact)
Datamax Inc. (El Dorado)
106 W. Main Street, Ste. 408
El Dorado, AR 71730
Main: 870.444.2537 (Contact)
Datamax Inc. (Fort Smith)
4311 Burrough Road
Fort Smith, AR 72916
Main: 479.782.5546 (Contact)
Datamax Inc. (Jonesboro)
3800 S Caraway Rd, Ste. 12
Jonesboro, AR 72404
Main: 870.663.4548 (Contact)
Datamax Inc. (Texarkana)
2221 N. State Line Avenue
Texarkana, TX 75501
Main: 903.336.6715 (Contact)
Datamax Inc. (Russellville)
1304 S Arkansas Avenue
Russellville, AR 72801
Main: 479.967.0381 (Contact)