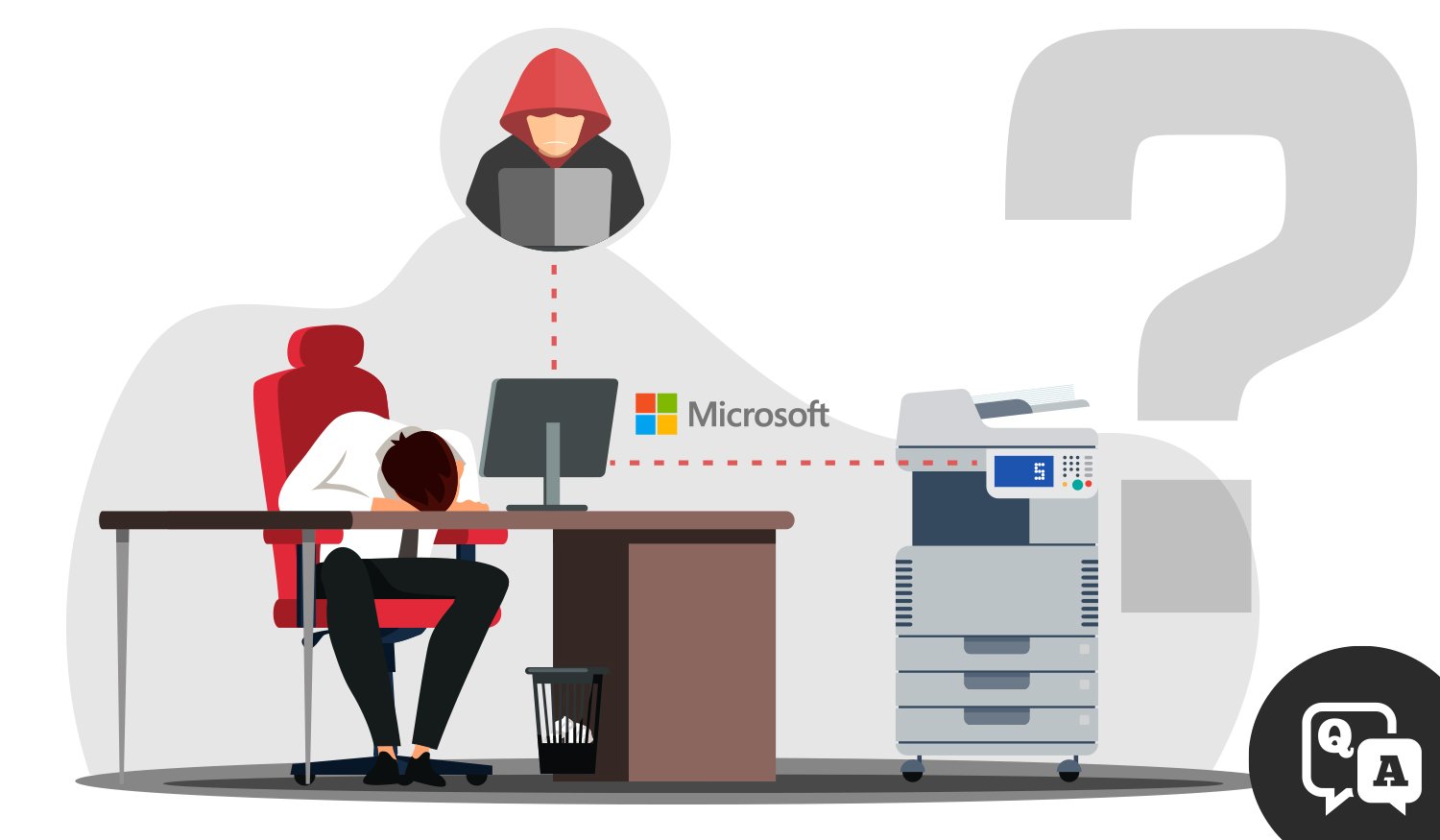
PrintNightmare is a bug in the Windows spooler service that can, under certain circumstances, allow an attacker to remotely run code on a Microsoft Windows system as the local system user.
The “PrintNightmare” vulnerability has circulated cybersecurity news recently, bringing with it concern and a number of questions for Windows users and, more specifically, those who print from a Windows system. Here’s what we know about this ongoing print security threat.
What is “PrintNightmare”?
Essentially, it is a bug in the Windows spooler service that can, under certain circumstances, allow an attacker to remotely run code on a Microsoft Windows system as the local system user. Potentially, anyone who uses a Windows computer and utilizes the Windows print spooler could be vulnerable.
What is a Print Spooler?
Print Spooler is a Windows service enabled by default in all Windows clients and servers. The service manages print jobs by loading printer drivers, receiving files to be printed, queuing them, and then scheduling them.
Are all Windows versions vulnerable?
Yes, all versions of Windows are vulnerable.
What can you do?
Patching your system is a powerful prevention method.
In addition to its regular updates, Microsoft has now released what it calls a “critical severity patch” for this vulnerability, and can be found via Windows Update or from an Advisory released by Windows earlier this month. Patch to all Microsoft Windows systems, but certainly any that have the print spooler service exposed to your network.
Additionally, this news serves as a prudent reminder to run ONLY versions of Microsoft Windows that still receive security support, and still receive automatic updates. More on that here.
Have questions?
We recommend your IT personnel read through the Microsoft Advisory to better understand possible mitigations for your business. Datamax is ready to answer your questions as well. To set up a meeting with a technology specialist and visit about your specific security preparation, please click below!



