
From document workflow, network security to print management and many things in between, our intent is to serve as a vehicle for helping YOU maximize YOUR technology investment.
Technology, much like life, moves pretty fast. If you don’t stop and look around once in a while, you could miss it.
We, the dedicated scribes of the Datamax Thinking Blog, certainly don’t want our readers to miss it. We work hard each year to contemplate, to evaluate and, ultimately, educate on many of the moving parts of an ever-changing business technology landscape. From document workflow, network security to print management and many things in between, our intent is to serve as a vehicle for helping YOU maximize YOUR technology investment.
In doing so, we certainly learn a lot every year about technology challenges and how to overcome them. We hope that you, loyal reader, can say the same.
With that, as we look forward to a new year of fresh ideas and further technology innovation, we take one final look back at the most read blogs published in 2018:
1. Canon’s Unified Firmware Platform: Full Speed Ahead in Existing Copier Models
 Visiting a car dealership (even if today, most buyers’ research is done online beforehand), there’s multiple variables to consider. Beyond budget and leasing options, one must consider speed (that sleek, streamlined sports car), functionality (the gas-friendly cross-over with room for the dog), safety/security, as well as that inevitable drop in value with that vehicle moving forward.
Visiting a car dealership (even if today, most buyers’ research is done online beforehand), there’s multiple variables to consider. Beyond budget and leasing options, one must consider speed (that sleek, streamlined sports car), functionality (the gas-friendly cross-over with room for the dog), safety/security, as well as that inevitable drop in value with that vehicle moving forward.
The same used to be said about copiers.
Traditionally, parallels exist between the two. New upgrades and features for Multifunction Printers were introduced by model exclusively, deeming your copier obsolete with every new feature introduced. But with Canon’s Unified Firmware Platform, you can have your speed and functionality, with little to no worry of impending value depreciation. Read more.
2. 7 Trustworthy Steps in Avoiding Ransomware, Phishing Scams
 Rock climbing is an endeavor built entirely around trust: Trust in your belayer. Trust in your equipment. Trust in the terrain surrounding you. And, of course, trust in yourself.
Rock climbing is an endeavor built entirely around trust: Trust in your belayer. Trust in your equipment. Trust in the terrain surrounding you. And, of course, trust in yourself.
Likewise, your organization’s online security often comes down to a matter of trust. But trust in this manner should never be earned without scrutiny, verification and due diligence.
Modern day attacks, from socially engineered to phishing email scams, are built entirely around the art of deception. Read more.
3. Document Workflow: 3 Ways to Blaze a Better Paper Trail
 Have you ever followed your own paper trail? Where does it lead you?
Have you ever followed your own paper trail? Where does it lead you?
Regardless of the size of your organization – a small work group up to a large enterprise - it has a unique paper trail based on your existing technology and individual departmental practices. Your routine document workflow, files and paper moving from desk to desk both manually and digitally, dictate the route of your trail. Your path can often be cluttered by manual, paper based processing, damaged by inadequate security measures or completely overgrown from simple negligence.
How navigable is your paper trail right now? How well is it aligned with your overall business objectives? It may be time to identify both current inefficiencies and explore cost-effective, fully secure practices moving forward.
Are you ready to become a paper trail blazer? Read more.
4. The Elephant in the (Waiting) Room: Why Your Healthcare Facility Needs a Security Risk Analysis Now
 For many health organizations, the elephant in the waiting room is still seated there, anxiously anticipating when it might be acknowledged or tended to.
For many health organizations, the elephant in the waiting room is still seated there, anxiously anticipating when it might be acknowledged or tended to.
That elephant is the Security Risk Analysis (SRA). Originally mandated by HIPAA and subsequently further enforced by government programs such as Meaningful Use and now the Medicare Access and CHIP Reauthorization Act (MACRA), the SRA is a vital component to both healthcare facilities’ ultimate livelihood and the confidential information of their clients. Read more.
5. Section 179 Deduction: Christmas Comes Early for Businesses Looking to Purchase Technology
 As the clock winds down in 2018, businesses are scanning the field for ways to close out the year on a winning note.
As the clock winds down in 2018, businesses are scanning the field for ways to close out the year on a winning note.
Small business owners or managers may not be aware of an incentive that could forge a huge technology and productivity boost in their immediate future: Section 179 Deduction of the IRS Tax Code.
This deduction could be a BIG gift for any small to medium sized business looking to make a technology purchase by year-end. But interested parties must move fast. Read more.
6. Healthcare Organizations Need a Roadmap to Navigate Cybersecurity
 All organizations are guilty of just “going through the motions” at times.
All organizations are guilty of just “going through the motions” at times.
A client services specialist leaning too heavily on his company script. The sales representative who meets her quota but fails to concentrate on continued professional development (aka, the learning zone). There are countless scenarios within a work place where crucial tasks are tackled without enthusiasm or a particular level of involvement.
But few, if any, carry the level of risk of a healthcare facility just going through the motions with its cybersecurity plan. The organization must navigate this landscape carefully, and with a trusted map that leads to long-term security and compliance for the unpredictable journey ahead. Read more.
7. HIPAA: Failure to Comply Could Mean Goodbye
 When it comes to your healthcare organization and HIPAA, failure (to comply) is not an option.
When it comes to your healthcare organization and HIPAA, failure (to comply) is not an option.
The monetary penalties associated with HIPAA violations, coupled with the potential costs of a data breach itself, leave covered entities that deal with Patient Health Information (PHI) and ePHI little choice but to develop a multi-layered, long-term Compliance and Security plan. The penalties, based on the level of negligence, could be detrimental. They could put your facility out of operation and you out of a job. Read more
8. 5 Expert Skills for Production Print Runs: Conquering the Double Black Diamond
 When it comes to Double Black Diamond runs, experts only dare exit the ski lift.
When it comes to Double Black Diamond runs, experts only dare exit the ski lift.
These heart-racing, often terrifying runs are characterized by exceptionally steep slopes, and other hazards such as narrow trails, high winds, and obstacles like steep drop-offs, rocks, moguls or trees. You may contemplate such slopes with hope, but you'll likely retreat with "nope."
The conditions that Production Printers face today can be equally harrowing. Shorter run lengths, mounting costs, increasing customer demand, and the constant pressure to plow through production with more speed and agility, are just a few of the challenges that make it difficult for print operators to stay straight-forward in their skis. Read more.
9. Print Pacesetter: In-House Production Offers You Control at Every Turn
 In the Indy Car racing circuit, road courses require superior braking systems that are able to handle intense, repetitive braking as cars approach sharp, hairpin turns.
In the Indy Car racing circuit, road courses require superior braking systems that are able to handle intense, repetitive braking as cars approach sharp, hairpin turns.
Often times, outsourcing your production print is a lot like racing behind the wheel of a 700-horse power, 2.2-liter twin turbo Indy Car with inferior brakes: It runs like clockwork until the unexpected happens (deadline change, color issue, mark-up fee) and you completely lose control.
From printing envelopes, marketing brochures and banners, healthcare books or business cards, organizations are discovering the distinct advantage of printing many of their jobs in-house. Read more.
10. Technology Forecast: Office Climate Change Imminent, but Probability of Printing Remains High
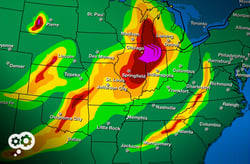 By 2020, Cisco’s Internet Business Solutions Group predicts that 50 billion physical IoT devices will be connected to the Internet, consuming, generating, and communicating data. The office is no exception.
By 2020, Cisco’s Internet Business Solutions Group predicts that 50 billion physical IoT devices will be connected to the Internet, consuming, generating, and communicating data. The office is no exception.
Crucial documents reside on our desks and file cabinets, but also in cloud servers and mobile devices. With such wide and easy access to the information we need, it’s tempting to think that printing may soon become a function of the past.
As ESPN analyst Lee Corso famously says on College Football Game Day, “Not so fast, my friend!” Read more.
Moving into 2019, we look forward to educating, collaborating, and sparking ideas for maximizing the technology that matters. Interested in keeping up with the Datamax Thinking Blog? Subscribe in the form at the top right of this page!

